Career Barriers
Understand how hiring trends and constraints impact your cybersecurity journey, and how to navigate them.
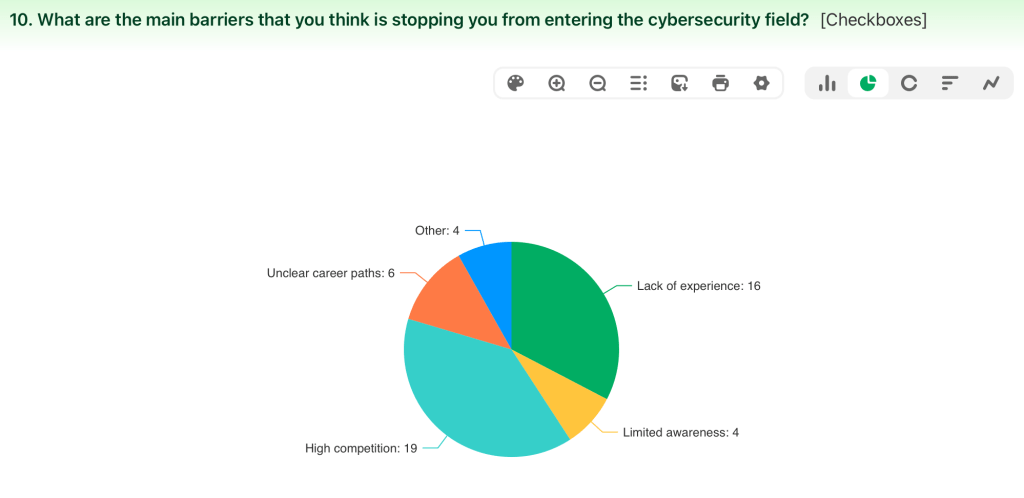
The piechart shows what barrier is stopping them from entering the cybersecurity job market and this leads to students being confused about where to start with their career choices.
Barriers
Cybersecurity students at Kingston University often face experience requirements, automated hiring filters, and limited local roles. This hub explains these barriers and offers strategies, resources, and pathways to help you enter and progress in the field.
| Barriers | Percentage of students responses | Support |
| Lack of Experience | 61.54% | The Foundation: CompTIA Security+ remains the gold standard for getting past initial screening, especially for government-adjacent roles. The SOC Path: If you want to be an analyst, look at CompTIA CySA+ or Blue Team Level 1 (BTL1). The “Support” Backdoor: If you can’t land a “Cybersecurity Analyst” role, take a Junior SysAdmin or Help Desk role at a company with a security team. Spend six months excelling at your job, then volunteer to help the security team with log reviews or patching. Internal transfers are the easiest way to break in. |
| Limited awareness | 15.38% | Use LinkedIn or any other useful platforms to find alumni from your university who are now in security. Ask for a “Coffee Chat” (virtual or in-person) to ask about their challenges. This builds awareness for them that you exist. |
| High competition | 73.08% | The 2:1 LinkedIn Rule: For every 2 jobs you apply for online, reach out to 1 person at a company you actually like. That conversation often leads to: “Actually, we have a junior role opening next month, send me your CV.” – Companies are desperate for people who know how to secure LLMs (Large Language Models) against prompt injection or data leakage. |
| Unclear career paths | 23.08% | Investigate: Do you like solving puzzles and finding out who did it? (Digital Forensics, Cyber Crime Investigation). – Protect & Defend: Do you like building walls and watching for intruders? (SOC Analyst, Incident Responder). – Analyse: Do you like looking at data to find hidden patterns? (Threat Intelligence, Data Analyst). – Oversee & Govern: Do you like rules, strategy, and business risk? (GRC, IT Auditor, Security Manager). |
| Other | 15.38% | Students should also work on personal projects to demonstrate their skills. For example, they can set up a home lab, perform vulnerability scans on their own systems, or simulate basic penetration testing activities. These projects can then be documented and added to a portfolio or GitHub. |